Linux安全配置杂文
发布时间:2014-09-05 14:14:54作者:知识屋
Linux安全配置杂文
SSH 配置
vim /etc/ssh/sshd_config <<VIM > /dev/null 2>&1
:s/#LoginGraceTime 2m/LoginGraceTime 2m/
:s/#PermitRootLogin yes/PermitRootLogin no/
:s/#MaxAuthTries 6/MaxAuthTries 3/
:%s$#AuthorizedKeysFile$AuthorizedKeysFile /dev/null$
:%s/GSSAPIAuthentication yes/GSSAPIAuthentication no/
:%s/GSSAPICleanupCredentials yes/GSSAPICleanupCredentials no/
:wq
VIM
禁止证书登陆 AuthorizedKeysFile /dev/null
锁定用户禁止登陆
passwd -l bin
passwd -l daemon
passwd -l adm
passwd -l lp
passwd -l sync
passwd -l shutdown
passwd -l halt
passwd -l mail
passwd -l uucp
passwd -l operator
passwd -l games
passwd -l gopher
passwd -l ftp
passwd -l nobody
passwd -l vcsa
passwd -l saslauth
passwd -l postfix
检查可以登陆的用户与有密码的用户
Java代码
#!/bin/bash
function section(){
local title=$1
echo "=================================================="
echo " $title "
echo "=================================================="
}
section "Check login user"
grep -v nologin /etc/passwd
section "Check login password"
grep '/$' /etc/shadow
section "Check SSH authorized_keys file"
for key in $(ls -1 /home)
do
if [ -e $key/.ssh/authorized_keys ]; then
echo "$key : $key/.ssh/authorized_keys"
else
echo "$key : "
fi
done
55.2.1. pam_tally2.so
此模块的功能是,登陆错误输入密码3次,5分钟后自动解禁,在未解禁期间输入正确密码也无法登陆。
在配置文件 /etc/pam.d/sshd 顶端加入
auth required pam_tally2.so deny=3 onerr=fail unlock_time=300
查看失败次数
# pam_tally2
Login Failures Latest failure From
root 14 07/12/13 15:44:37 192.168.6.2
neo 8 07/12/13 15:45:36 192.168.6.2
重置计数器
# pam_tally2 -r -u root
Login Failures Latest failure From
root 14 07/12/13 15:44:37 192.168.6.2
# pam_tally2 -r -u neo
Login Failures Latest failure From
neo 8 07/12/13 15:45:36 192.168.6.2
pam_tally2 计数器日志保存在 /var/log/tallylog 注意,这是二进制格式的文件
例 55.1. /etc/pam.d/sshd
# cat /etc/pam.d/sshd
#%PAM-1.0
auth required pam_tally2.so deny=3 onerr=fail unlock_time=300
auth required pam_sepermit.so
auth include password-auth
account required pam_nologin.so
account include password-auth
password include password-auth
# pam_selinux.so close should be the first session rule
session required pam_selinux.so close
session required pam_loginuid.so
# pam_selinux.so open should only be followed by sessions to be executed in the user context
session required pam_selinux.so open env_params
session optional pam_keyinit.so force revoke
session include password-auth
以上配置root用户不受限制, 如果需要限制root用户,参考下面
auth required pam_tally2.so deny=3 unlock_time=5 even_deny_root root_unlock_time=1800
55.2.2. pam_listfile.so
用户登陆限制
将下面一行添加到 /etc/pam.d/sshd 中,这里采用白名单方式,你也可以采用黑名单方式
auth required pam_listfile.so item=user sense=allow file=/etc/ssh/whitelist onerr=fail
将允许登陆的用户添加到 /etc/ssh/whitelist,除此之外的用户将不能通过ssh登陆到你的系统
# cat /etc/ssh/whitelist
neo
www
例 55.2. /etc/pam.d/sshd - pam_listfile.so
# cat /etc/pam.d/sshd
#%PAM-1.0
auth required pam_listfile.so item=user sense=allow file=/etc/ssh/whitelist onerr=fail
auth required pam_tally2.so deny=3 onerr=fail unlock_time=300
auth required pam_sepermit.so
auth include password-auth
account required pam_nologin.so
account include password-auth
password include password-auth
# pam_selinux.so close should be the first session rule
session required pam_selinux.so close
session required pam_loginuid.so
# pam_selinux.so open should only be followed by sessions to be executed in the user context
session required pam_selinux.so open env_params
session optional pam_keyinit.so force revoke
session include password-auth
sense=allow 白名单方式, sense=deny 黑名单方式
auth required pam_listfile.so item=user sense=deny file=/etc/ssh/blacklist onerr=fail
(免责声明:文章内容如涉及作品内容、版权和其它问题,请及时与我们联系,我们将在第一时间删除内容,文章内容仅供参考)
相关知识
-
linux一键安装web环境全攻略 在linux系统中怎么一键安装web环境方法
-
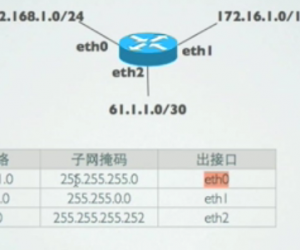
Linux网络基本网络配置方法介绍 如何配置Linux系统的网络方法
-
Linux下DNS服务器搭建详解 Linux下搭建DNS服务器和配置文件
-
对Linux进行详细的性能监控的方法 Linux 系统性能监控命令详解
-
linux系统root密码忘了怎么办 linux忘记root密码后找回密码的方法
-
Linux基本命令有哪些 Linux系统常用操作命令有哪些
-
Linux必学的网络操作命令 linux网络操作相关命令汇总
-
linux系统从入侵到提权的详细过程 linux入侵提权服务器方法技巧
-
linux系统怎么用命令切换用户登录 Linux切换用户的命令是什么
-
在linux中添加普通新用户登录 如何在Linux中添加一个新的用户
软件推荐
更多 >-
1
 专为国人订制!Linux Deepin新版发布
专为国人订制!Linux Deepin新版发布2012-07-10
-
2
CentOS 6.3安装(详细图解教程)
-
3
Linux怎么查看网卡驱动?Linux下查看网卡的驱动程序
-
4
centos修改主机名命令
-
5
Ubuntu或UbuntuKyKin14.04Unity桌面风格与Gnome桌面风格的切换
-
6
FEDORA 17中设置TIGERVNC远程访问
-
7
StartOS 5.0相关介绍,新型的Linux系统!
-
8
解决vSphere Client登录linux版vCenter失败
-
9
LINUX最新提权 Exploits Linux Kernel <= 2.6.37
-
10
nginx在网站中的7层转发功能